Bitcoin Cash Considers Prisoner's Dilemma
The Prisoner's Dilemma
Game theory is the study of one or more actors. The actors engage in a competitive or collaborative activity. At the end of the activity each actor has a way to judge the outcome and compare the outcome to other outcomes.
Game theory applies to:
traders on the market
dating
mining cryptocurrency
Traditional games (chess, bridge, etc.)
as well as many other situations. Not every player needs to be judged the same way. For an example, consider Leslie who goes to the market and buys a peck of apples from an apple farmer, Edna, for $4. Edna most likely valued the apples sold at less than $4. As Edna has lots of apples and would like to sell them before they rot. Leslie wanted the apples so much she not only parted with $4 but decided to use her time to seek out apples.
In game theory the value that each actor puts on each outcome is called a utility function. In our example Leslie might find the utility of laving the market with a peck of apples to be more than the Edna, who has apples at home. Utility is intended to be a measure of the value, or the enjoyment, or the use of an item or situation. Utility could be a subjective concept, but is useful when comparisons can be made.
In game theory there is a very famous example of a game known as the prisoner's dilemma. This situation happens when two sisters rob an electronics store. The police find each one of them driving a van full of stolen big screen TVs. Each of the sisters is arrested and taken in for questioning without the opportunity to talk to the other sister. The police then give each sister a choice. The choice is to tell on their sister and receive a year off any prison sentence. As it stands, each sister is facing a year of jail time for possessing the stolen televisions. The table below explains the consequences of the sister's option to stay silent or defect from her family.
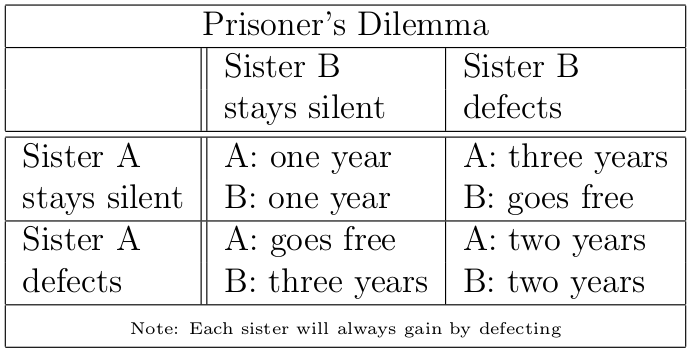
Now, basically the best outcome for both sisters for each of them to stay silent. That's the outcome that has the least amount of total jail time. However this outcome is unstable. In the case that both sisters stay quiet either one will gain (go free) from defecting. And even if one sister defects the situation is still unstable as the other sister could serve two years instead of three by telling. In fact each sister is always better off by defecting, no matter what the other one does. If both sisters do defect then neither sister can improve their outcome by their choice alone.
This game provides some insight into why, in some cases, corporative solutions are never sought after.
A Modest Proposal of Some Bitcoin Cash Miners
A proposal of Jiang Zhuoer and signed by other miners has been made to the Bitcoin Cash community. This proposal encourages other miners to orphan blocks that do not provide for a fund for developers. The proposal has a clear begin date and end date.
The proposal claims that it is not a change in the protocol. However, it would be a change in "a set of conventions governing the treatment of data in an electronic communication system." Which is a change in protocol according to Merriam-Webster. I think the author of the proposal meant that this proposed change in protocol would not be hard coded in the client.
It is the very fact that this protocol change is not hardcoded allows for this game theoretic analysis. We hope to understand the game theoretic implications of this type of protocol change.
Miner Behavior
Clearly there is anecdotal evidence that some people support funding developers in the form of the proposal. There is also anecdotal evidence here and here that some people don't support the proposal. Even better, is the fact that SHA256 mining allocation is very well understood and miners generally go after the most profit. cite: Bissias, Levine, Thibodeau.
For our game theoretic analysis we assume that 30% of the miners are ideologically driven in favor of the proposal. They assign a high utility to all blocks funding developers. The exact amount of value they assign the dev fund does not effect this analysis. The people who support the dev fund expect that this fund will pay off in the future in the form of a higher price. Economists would say that people that support the proposal have a low time preference. Also miners that support the proposal have a higher risk tolerance, as the dev fund is, in effect, investing in a startup. As we understand miners risk tolarance to be quite low (Bissias, Levine, Thibodeau) we expect that 30% is an overestimate.
We assume that all other miners are maximizing (revenue and therefore) profit.
The Game
If the 70% of miners that are profit maximizing know that they will all act together, then they can sleep easy knowing that following the longest chain and ignoring dev funding will maximize their profit. However, just like the electronics thief sister being questioned, the miners don't know if their sister miners will defect to the other side or not. As we will see, one major advantage is that the miners can coordinate their action. They can talk to each other.
As simplifying assumptions we assume that the 30% in favor of the dev plan always mine a chain consistent with the dev funding. To explain the incentives we break the profit seekers down into group A which is 30% of the hashing power and group B which is 40% of the hashing power. In such a case we have
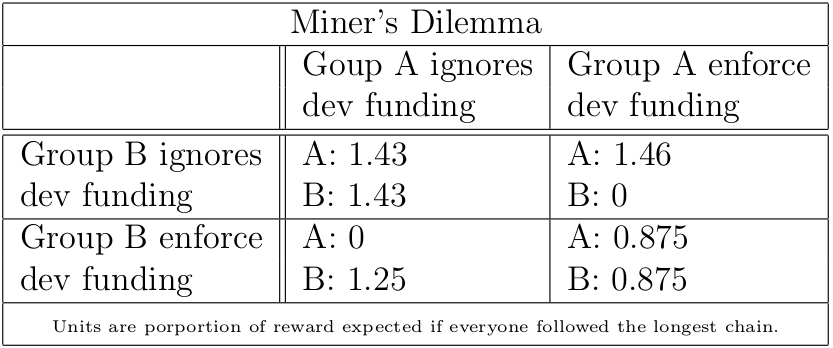
From this table we can see that if 30% (and not less than 20%) of the profit seeking miners enforce dev funding they will profit more. However, if 40% of the miners enforce dev funding then they will all collectively loose. However, if the longest chain is enforcing the dev funding then it's in everyone's interest to switch.
This analysis ignores the fact that BCH is a minority chain. Considering this fact, it's likely that hashing power would be attracted or repelled from BCH to balance out the profitability. This is asserted in the dev funding proposal, and to a very good approximation is correct.
The Sisters Talk
We're talking about miners on a public blockchain. They are not being held incommunicado like our sisters above. Mining participants could advertise the protocol they follow in the version number of a block that they mine. This could go both ways.
Miners like Jiang Zhuoer that want to fund the developers could flip a bit in their version number and if a sufficient number of blocks signal for the protocol rule at the scheduled MTP then dev funding could be safely enforced.
It works the other way as well. Miners that want to follow the longest chain could signal that with a bit in the version number. As long as a sufficient number of miners signal they are mining the longest chain then miners can safely add to the longest chain.
There is the opportunity that miners could lie. However, most of the time, lying in this circumstance does not help your cause. For more information about using the version number to signal the desired protocol to mine see BIP0009.
Conclusions
Having a consensus rule that is not enforced by the nodes leads to some very interesting game theory. If the consensus rule is enforced by all nodes than it would be in every miners interest to enforce the rule on that chain. However, if the consensus rule is controversial then there is a serious risk of forking off yet another minority chain.
Perhaps the best that can be hoped for is that both sides agree on one bit of the version number. Then use that bit to signal if funding for developers is enforced or not. As long as both sides can accept the results of the miner's vote then then the current Bitcoin Cash network does not risk a split.
To be clear, using a version bit to signal which protocol to follow may result in a genuine compromise. That is, a situation where the dev fund is only funded some of the six months that is asked for.
To me using a bit in the version is the polite way to mediate this dispute.
 Darren Tapp
Darren Tapp